This section will describe the assessment process for VE and conflict and highlight the different types of tools that are currently available to support your assessments. Also, this section will provide additional resources on how to implement these tools in your environment. Note that the featured tool – USAID’s Guide to the Drivers of Violent Extremism from 2009 – focuses on the “drivers” rather than the “dynamics” of violent extremism. Now, donors and practitioners consider the importance of examining VE dynamics in addition to the drivers. The conflict assessment tools described below can be adapted to examine VE dynamics as well.
What is this tool?
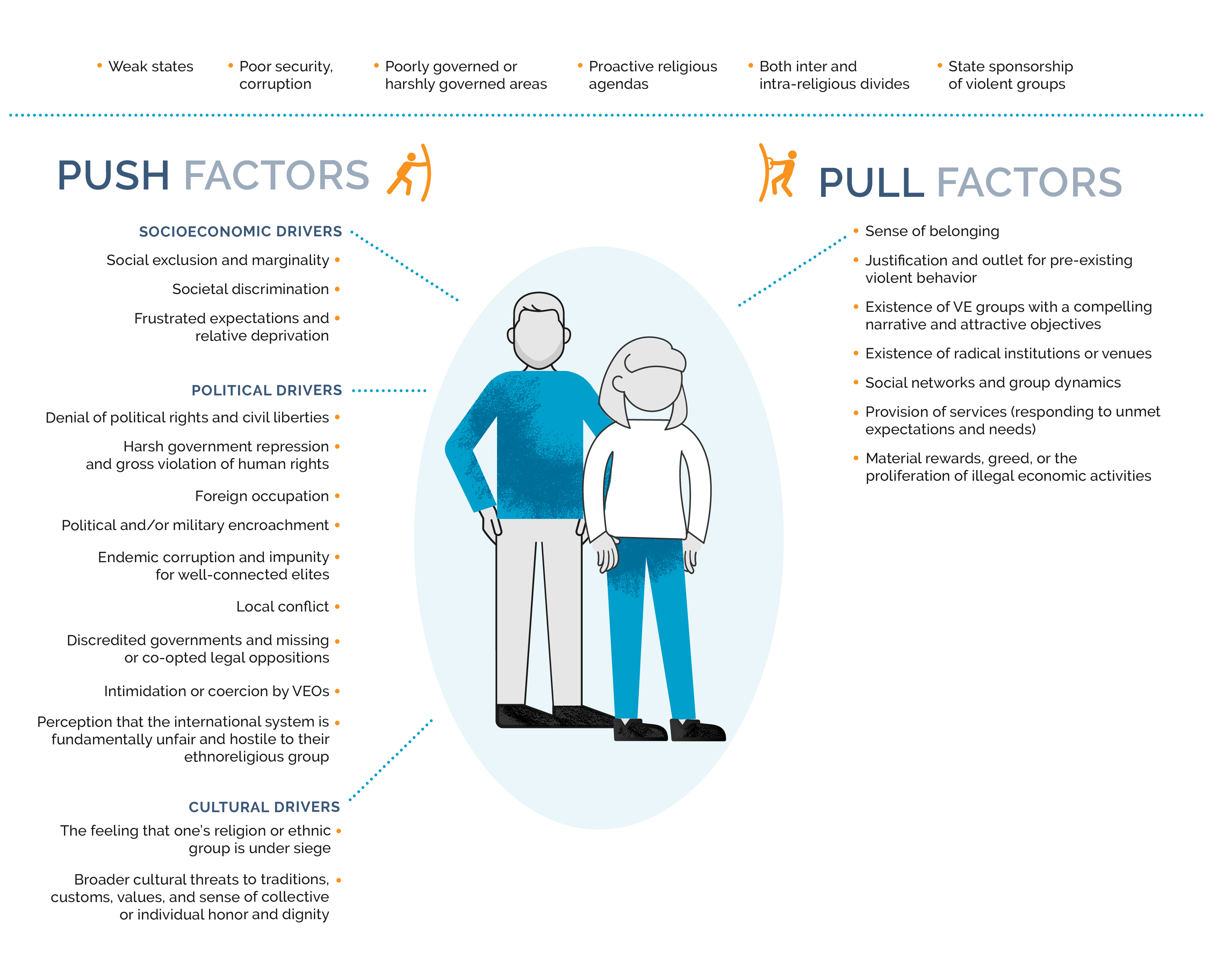
This guide is a key framework for much of USAID’s P/CVE programming. Although there is no set profile for violent extremists, and radicalization pathways are rarely straight lines, this guide and its push/pull model is one way of analyzing why people join VEOs.
How does this relate to your activity?
This framework helps you understand the factors that motivate people to join VEOs as well as how these factors may vary among different vulnerable groups. However, the model does not look at resilience factors within a community or factors that help strengthen an individual’s ability to resist the pull of violent extremism.
When do you want to apply it?
This assessment should be conducted before you design your project. Understanding VE drivers will help you think about the factors that may be relevant for the specific community or group your project is trying to reach. This assessment framework is also very useful for designing interventions, off-ramp and reintegration, and rehabilitation programs to understand why people leave VE groups and what support they might need in order to do so.
Find this in our resource library
The graphic below provides an overview of the push/pull model derived from USAID’s Guide to the Drivers of Violent Extremism. The graphic shows the enabling environment for VE, push factors (which impel individuals to join a VEO) and pull factors (features that individuals find attractive about the group).

While the push/pull model is a widely recognized framework for understanding radicalization, radicalization pathways to violence are very complex and require more than one analytical lens. Additional examples of frameworks that explore radicalization include:
-
Framework(s): VE Factors Nexus and Vulnerability and ResilienceSource: UNDP and International Alert
-
Framework(s): The CVE CycleSource: Hedayah
-
Framework(s): Push Factors, Group Dynamics and Relationships, Pull Factors and Sources of ResilienceSource: Search for Common Ground and Hedayah
-
Process of Radicalization Leading to Violence and Factors Leading to Violent RadicalizationSource: Centre for the Prevention of Radicalization Leading to Violence
Radicalization is not a linear process, particularly as people and groups respond to changes in the environment around them. To supplement an analysis of VE dynamics and drivers, it is important to think about the broader conflict dynamics. It is equally important to identify sources of resilience and connection that strengthen people's abilities to withstand the draw of VE. There are several different tools you can use to conduct a conflict analysis, and these can also be adapted to examine VE dynamics.



Many different data collection methodologies can help you to assess the drivers of VE and conflict, including quantitative (surveys) and qualitative (focus group discussions) methods. Each type of methodology has strengths and weaknesses. Often a combination of both methodologies (mixed-methods) leads to a more robust assessment. The appropriateness of such an approach may be shaped by the environment and your organization’s resources, research capabilities, familiarity with the context, and timelines. It is always recommended to engage researchers who are trained in these methodologies, understand the ethical implications of research involving human subjects, and have prior field-based research experience in sensitive and conflict-affected environments.
The Asia Foundation’s resource: Survey's and Countering Violent Extremism: A Practioner Guide provides a useful overview of quantitative versus qualitative methods in Table 1 below. Links to additional toolkits and guides for conducting research on VE can be found in the Resource Library.
Table 1: Quantitative vs. Qualitiative Methods
| Surveys/Quantitative | Qualitative Methods |
|---|---|
| Systematic data gathered from respondents by trained enumerators in a standardized and scripted way | Interviews, focus groups, observation, and written materials |
| Quantify answers to enable mathematical analysis | Rely on researchers to follow up on leads and more open-ended |
| Aim to make claims that can be generalized to a broader population | Focus on smaller number of individuals but in more depth |
| Enable us to see patterns in violent extremist events, behaviors, and attitudes. | Illuminate processes and mechanisms of radicalization |


Everyone has different perspectives that could impact their ability to remain objective, so always consider whether biases may impact an assessment. This could mean a personal bias you may have or a respondent’s bias that impacts their answers to your questions.
Here are a few questions to consider before and during your research to reflect on potential biases that could influence the outcome of your assessment:
Reducing our bias
- What motivates this assessment? Why we you conducting this assessment, and what is it meant to inform?
- How does our background affect our analysis of facts? What are key assumptions, and have they been tested?
- What can we miss or misinterpret because of our background? Are there alternative views?
- What is the needed level(s) of analysis (national, community, individuals, etc.)?
- How can we mitigate doing any potential harm in the way we conduct our assessment?
Identifying potential bias of our respondents and assessing source credibility
- What are our sources of information? Has data been triangulated by other sources or means of data collection?
- How many different types of stakeholders or stakeholder groups are engaged in our research? Are we seeking out different perspectives?
- Who is providing us information? What is their motivation for providing us this information?
- How did they access this information (i.e., do they have direct knowledge or is this hearsay from second- or third-hand sources)?
- In what setting are they providing us this information? Could that impact what information they are providing to us and why they are providing us this information?